Your cloud has an ROI problem
CloudBolt helps organizations be more efficient, agile, and value-driven in the cloud.
What we're solving
Are you reaching the full potential of your cloud?
Don’t just take our word for it
CloudBolt is transforming the way we manage our cloud resources by simplifying our automation and orchestration tasks, while their FinOps integration is giving us better control over costs.
This level of partnership and shared direction has enabled Home Depot to move faster, move further, and continuously enhance our offerings to our customers.
Working with CloudBolt has been a positive experience for all members of the Data#3 team, be it sales or service delivery.
But essentially what we did was took a process that took them about 48 hours on a really great week, down to about three or four minutes to deliver a full workload with security built-in.








































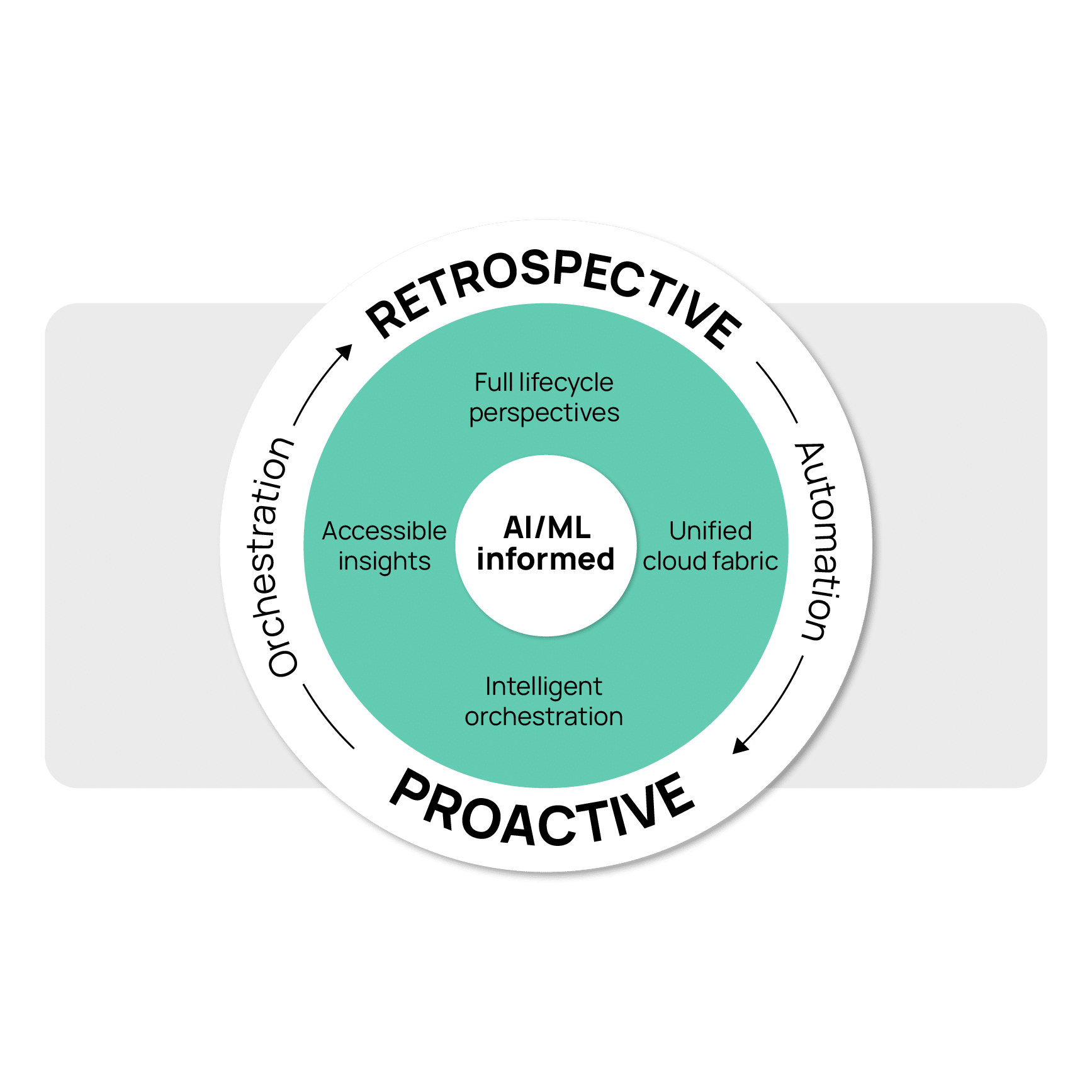
Hello Augmented FinOps
Learn More
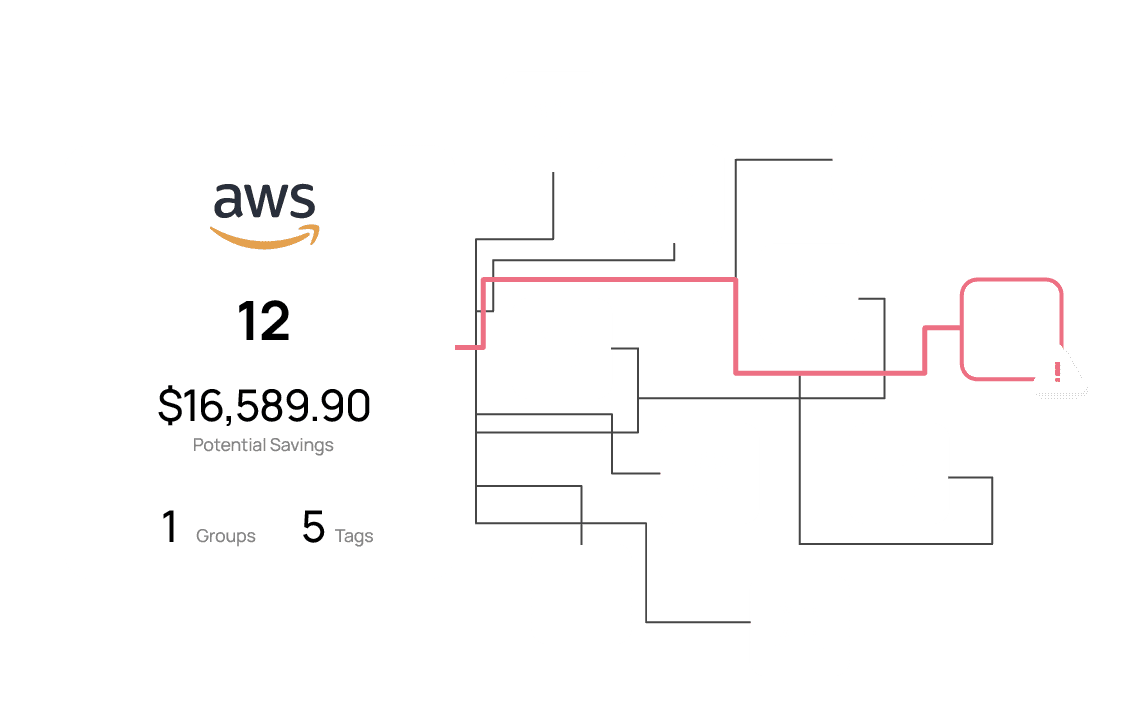
Map every cost back to your business
The complexity of handling multiple cloud platforms and inaccurate tagging results in unallocated costs and diminished accountability. CloudBolt normalizes financial data, ensuring you have complete cost traceability and precise allocation customized to your organization’s needs.
Learn more
Incorporate guardrails into every cloud action
Without proper controls, making costly decisions that don’t deliver desired returns is too easy in the cloud. With CloudBolt, your team can promote cost-effective, value-centric actions by integrating governance models into every stage of the resource lifecycle.
Learn more
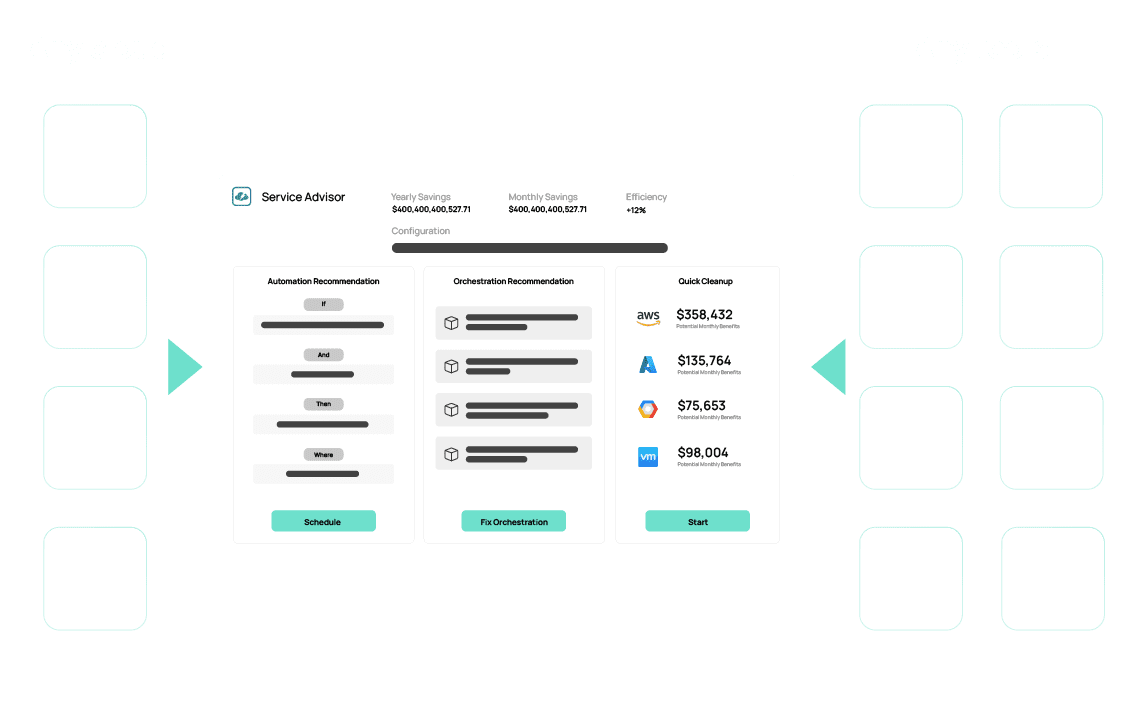
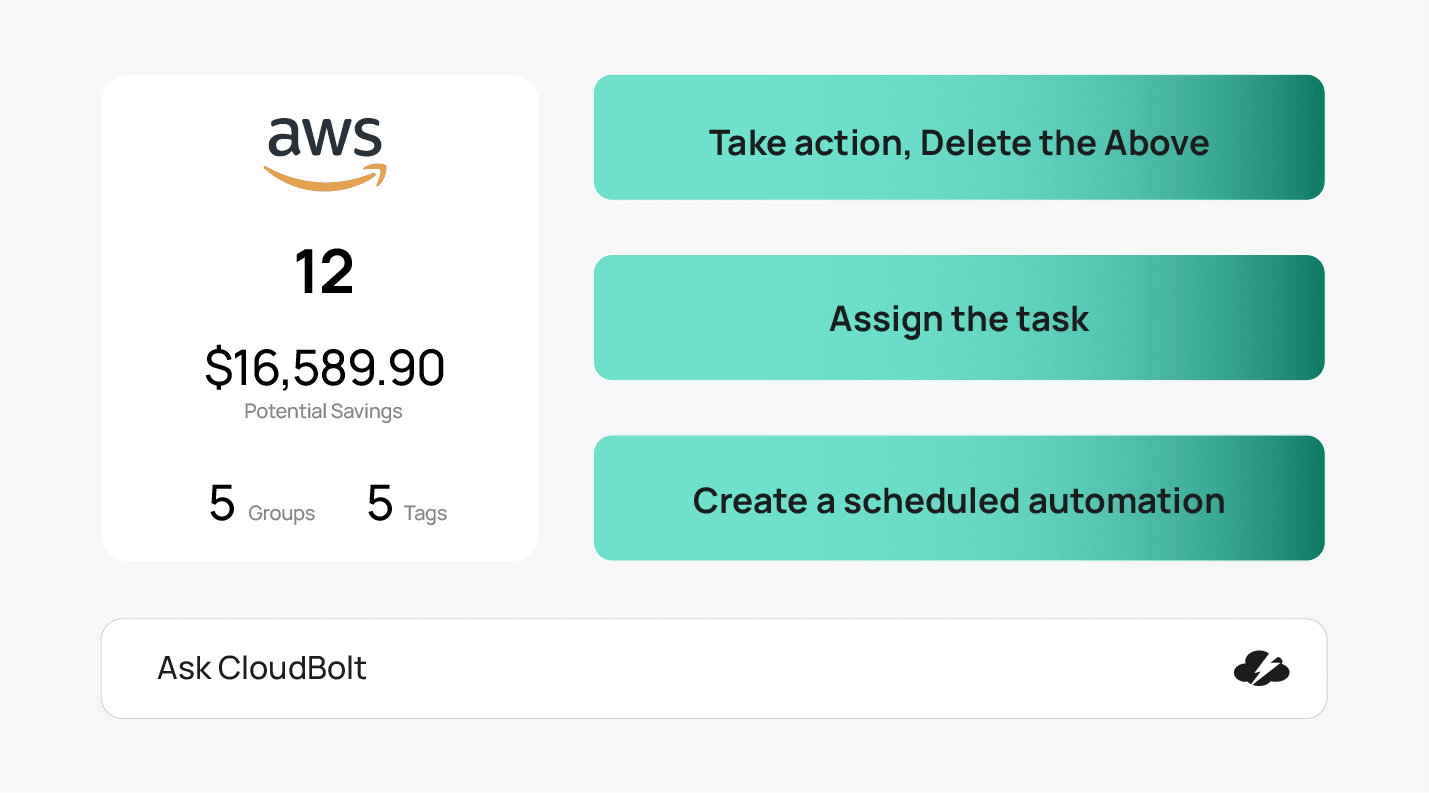
Accelerate insight to impact
Automation aims to simplify cloud waste remediation at scale, yet current approaches go unused because they’re too rigid or underpowered. CloudBolt offers flexible automation that integrates with your unique tools and processes so you can quickly resolve cost anomalies and reduce waste.
Learn more
Harness the power of assisted intelligence
Getting the right insights to the right people at the right time to make better cloud decisions is not easy. CloudBolt is harnessing AI to offer deeper, more insightful analysis, significantly reducing the cognitive load required to equip all cloud consumers with actionable financial insights.
Learn more
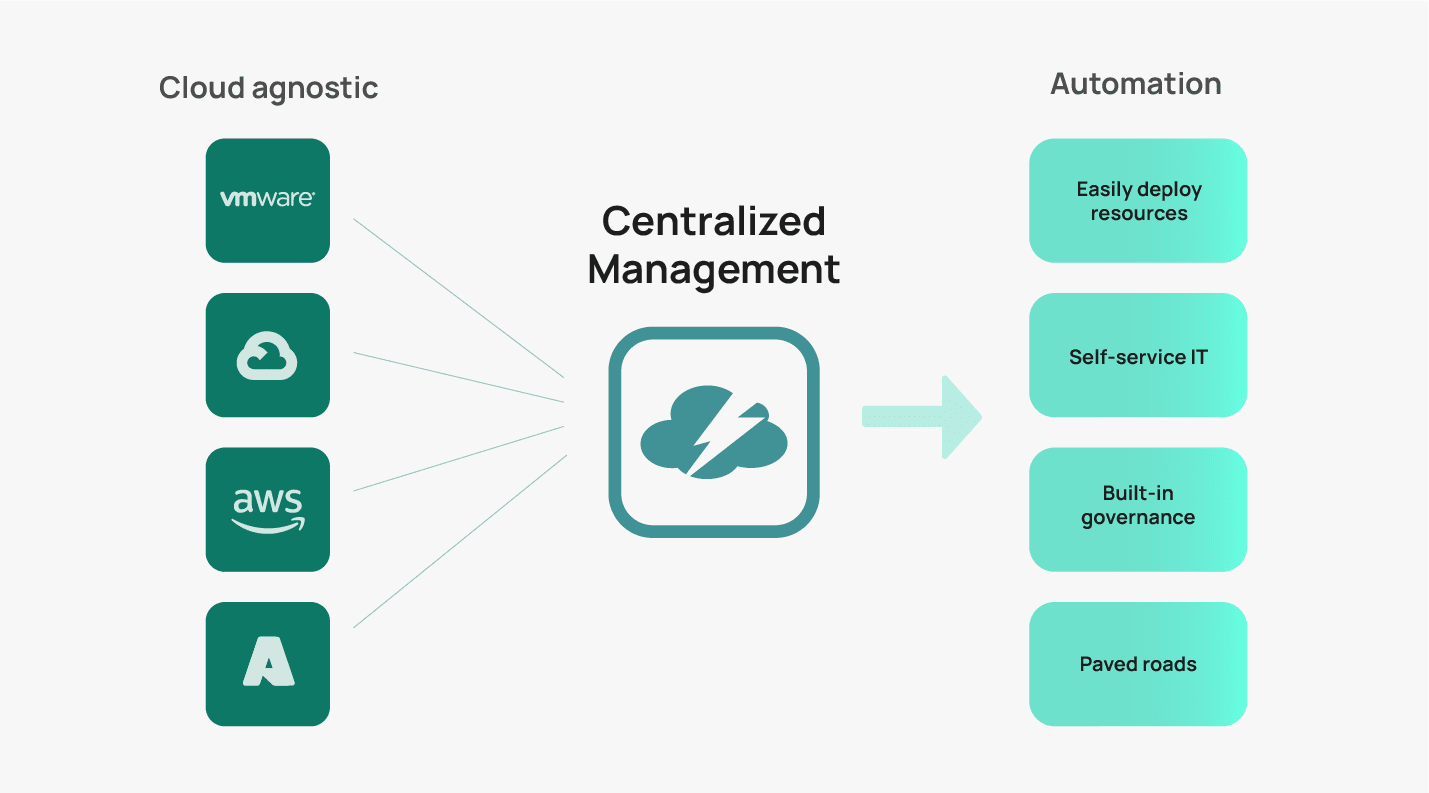
Operate the cloud your way
Cloud has become the sum of all compute resources – public/private/edge/sovereign. Only CloudBolt has the power to seamlessly automate and orchestrate across it all so that your cloud becomes a unified fabric that helps you finally put the “R” in ROI.
Learn more
CloudBolt’s Augmented FinOps featured in Forbes
Read now
Featured resources
Augmented FinOps: The Next Era for Cloud Cost Management
Augmented FinOps is an innovative approach that integrates artificial intelligence with financial operations, aiming at optimizing cloud cost management. This resource is specifically crafted for IT leaders, financial experts, and those keen on understanding and implementing pioneering strategies in cloud computing. In This White Paper, You Will Discover: Key Topics Explored: Transform Your Cloud Financial […]
The Truth About Cloud Value
Are you navigating the complexities of cloud transformation and seeking effective strategies to optimize your investments? This white paper is an essential resource for understanding the financial realities of cloud transformation strategy. It’s designed to guide enterprises through the intricacies of cloud computing, debunking common myths and setting the stage for successful cloud adoption. In […]
See CloudBolt in action
Request a demo